1. Methodology
The following four freeware memory image acquisition tools for Windows were evaluated on a physical machine with Intel(R) Core(TM) i7–6700HQ CPU @ 2.60GHz processor, 16GB of DDR4–2133MHz SO-DIMMs running 64-bit Microsoft Windows 10 Home on a Samsung 860 EVO SATA 2.5" 500GB SSD:
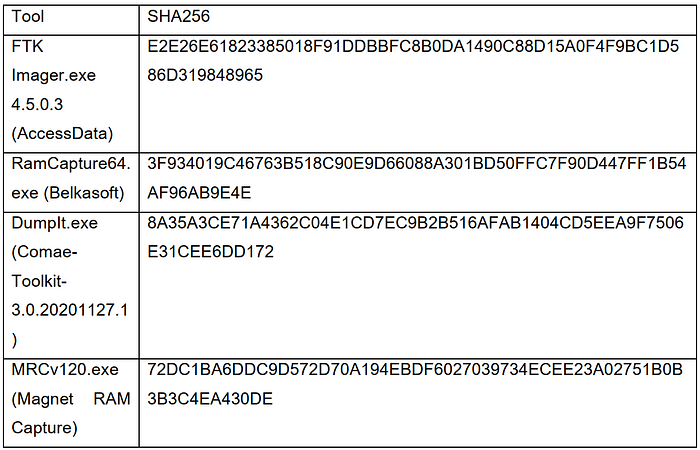
Since Medium does not officially support tables yet, I have posted them as pictures in this article.
When executing each tool, it was ensured that the same processes were running to have a common baseline when conducting the analysis. The machine was connected to the Internet when memory was acquired. They were evaluated based on the following criteria:
1. User interface and customizability
2. Acquisition time
3. Occupied memory according to Task Manager
4. Loaded DLLs
5. Registry changes and invoked files
6. Portable software
1.1 Output
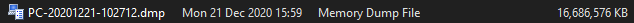
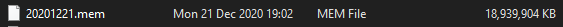

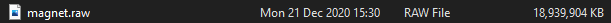
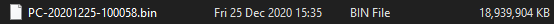
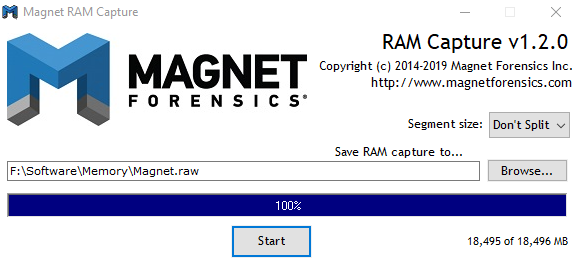
The above screenshots display the output from the four tools. The discrepancy in size between the captures from DumpIt and other tools is because of the file formats. DumpIt uses .dmp which is a memory dump file whereas all the other tools output in raw format which can result in larger output files than the actual size of physical RAM installed (BlackBag, 2016).
DumpIt also offers the option to capture memory in raw format as shown below although the developers discourage it. DumpIt’s statistics in the following section is based on its memory dump file capture and not raw capture as that is the tool’s default output format.

2. Discussion
2.1 User interface and customizability
Out of the selected tools, all tools except DumpIt have a graphical user interface (GUI). FTK Imager’s “File” menu has an option called “Capture Memory” to capture memory. Afterwards the path and the name of the output can be specified. It also provides an option to capture the page file.


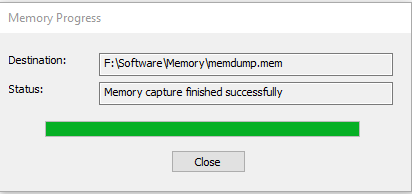
Belkasoft provides the option to specify the output location and has a button called “Capture” that is used to start the memory acquisition process. It does not provide the option to name the output, although this can be renamed later.

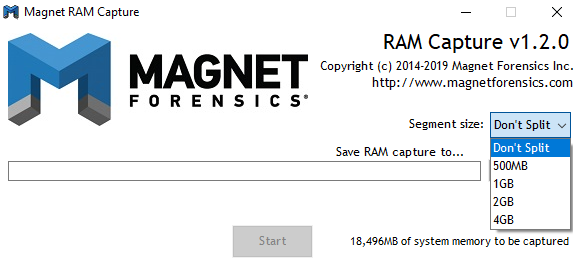
Magnet RAM Capture also provides the option to specify the path and name of the output. In addition, it offers the option to split the capture into 500MB, 1GB, 2B or 4GB segments. All these tools display a progress bar as well.
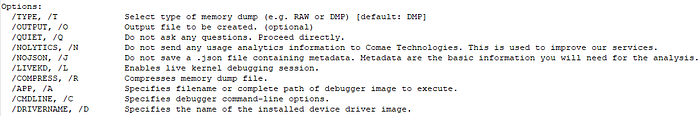
DumpIt was executed via PowerShell. Out of the tools tested, DumpIt provides the most variety of options through its commands.

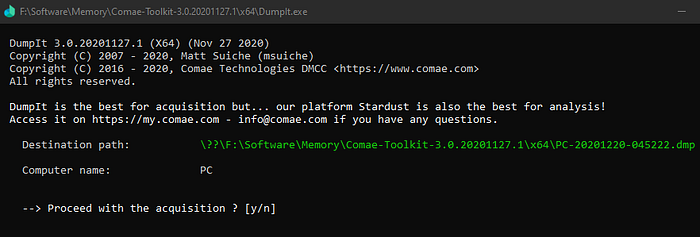
2.2 Acquisition time
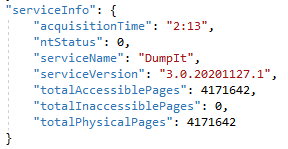
The time was calculated manually using an external stopwatch. For DumpIt, the acquisition time was also obtained from the json file output by the tool. The time obtained manually and from the json file were the same for DumpIt. All GUI-based tools outperformed DumpIt.
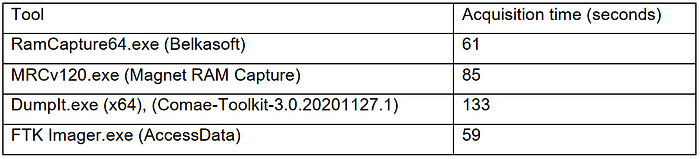
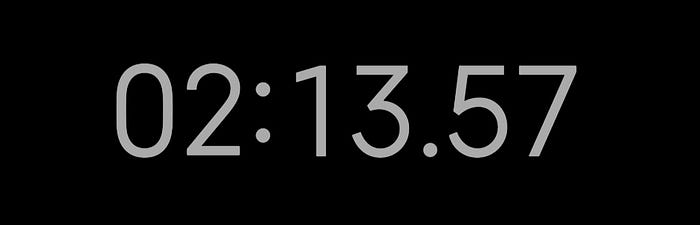


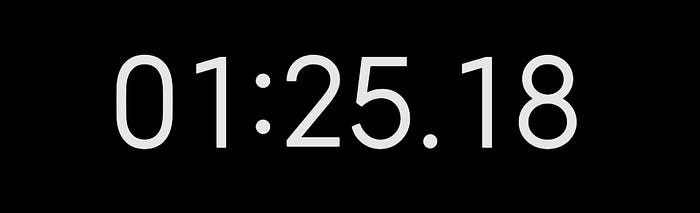
FTK Imager was the quickest, with Belkasoft just a couple of seconds behind. Despite being a command line tool, DumpIt took the longest time.
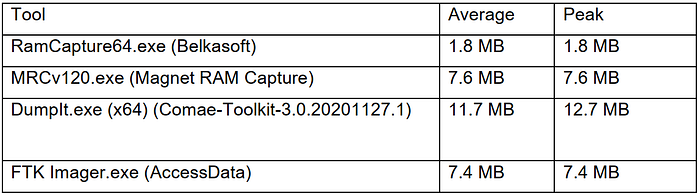
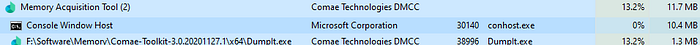
2.3 Occupied memory according to Task Manager
While the tools are being executed to capture the memory, the tools themselves will also use a portion of the memory to perform the capture. This can result in the creation of unwanted artefacts on the memory, which can result in important data being overwritten. Therefore, the amount of memory occupied by the tool is a vital metric to consider when choosing a memory acquisition tool.
Task Manager was used to monitory memory usage. Except for DumpIt, the memory usage of the tools remained consistent throughout the imaging process. DumpIt results in a small peak at the end of the process, which may be attributed to the creation of a .json file containing metadata regarding the capture as it is the only tool to output such a file.



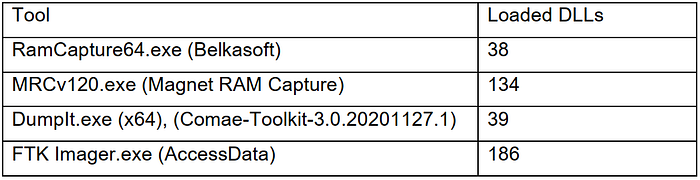
2.4 Loaded DLLs
When capturing memory, the tools will load some DLLs. The more DLLs invoked the more the possibility for unwanted artefacts to overwrite important data.
Process Explorer was used to identify loaded DLLs (froglogic, 2020).
RamCapture64, despite being a GUI tool, invoked the least number of DLLs. DumpIt being a command line tool invoked the second least number of DLLs. The other two GUI tools invoked more than 100 DLLs. FTK Imager loaded the highest number of DLLs. This could be expected as it is a GUI tool that offers various functionalities apart from just capturing memory. Screenshots aren’t provided for this metric as there are too many records.
2.5 Registry changes and invoked files
While these tools are being executed, they make changes to Windows registry keys and invoke resident files located in the hard drive. Therefore, both these factors must be considered when selecting the desired tool to use.
Process Monitor was used to identify modified registry keys and invoked files. The filter ‘RegSetValue’ was applied to Process Monitor to identify registry keys modified by the processes (Heddings, 2019). The filter ‘CreateFile’ was applied to Process Monitor to identify files invoked by the processes. Screenshots aren’t provided for this metric as there are too many records.
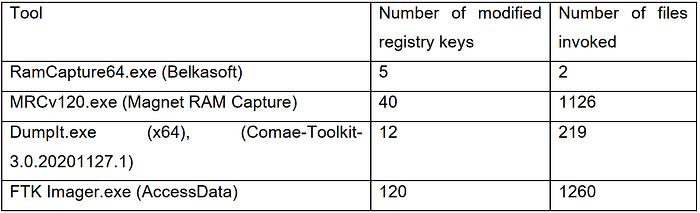
The order of ranking of tools is the same compared to loaded DLLs.
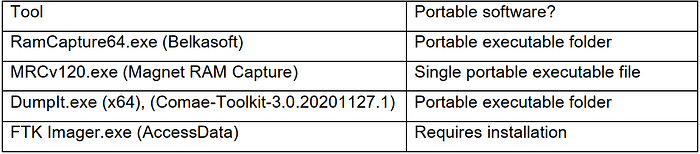
2.6 Portable software
Portable software are more convenient than software that require installation. Portable memory acquisition software can especially be useful for memory acquisition on-the-fly. Out of the four tools, only FTK Imager requires installation. Magnet RAM Capture only has a single executable file.
3. Evaluation
The tools are ranked here based on the most objective metrics. Thus, user interface and customizability and portable software are left out as they can be somewhat subjective.
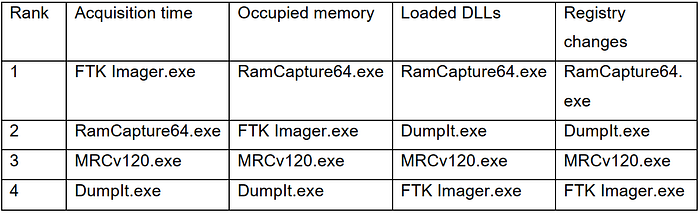
I find it hard to give an overall ranking for all the tools since I would have to assign a weighted grade for each metric which can be quite subjective. Yet, it is quite evident that based on the four metrics above, Belkasoft’s Live RAM Capturer is the best memory acquisition tool out of the four tools. That being said, this comparison is obviously not exhaustive.
References
BlackBag, 2016. Windows Memory Forensics — Part 2 | BlackBag. [Online]
Available at: https://www.blackbagtech.com/blog/windows-memory-forensics-part-2/
[Accessed 25 December 2020].
froglogic, 2020. Getting a list of DLLs currently loaded in a process. [Online]
Available at: https://kb.froglogic.com/misc/getting-list-of-loaded-dlls/
[Accessed 21 December 2020].
Heddings, L., 2019. SysInternals Pro: Using Process Monitor to Troubleshoot and Find Registry Hacks. [Online]
Available at: https://www.howtogeek.com/school/sysinternals-pro/lesson5/
[Accessed 20 December 2020].
